matterlogoboss
Cisco Asdm 7.2
Network Object NAT (ASA 8.3 and Later)All NAT rules that are configured as a parameter of a network object are considered to be network object NAT rules. Network object NAT is a quick and easy way to configure NAT for a single IP address, a range of addresses, or a subnet.
After you configure the network object, you can then identify the mapped address for that object.This chapter describes how to configure network object NAT, and it includes the following sections:.Note For detailed information about how NAT works, seeInformation About Network Object NATWhen a packet enters the ASA, both the source and destination IP addresses are checked against the network object NAT rules. The source and destination address in the packet can be translated by separate rules if separate matches are made.
These rules are not tied to each other; different combinations of rules can be used depending on the traffic.Because the rules are never paired, you cannot specify that a source address should be translated to A when going to destination X, but be translated to B when going to destination Y. Use twice NAT for that kind of functionality (twice NAT lets you identify the source and destination address in a single rule).For detailed information about the differences between twice NAT and network object NAT, see.Network object NAT rules are added to section 2 of the NAT rules table. For more information about NAT ordering, see. Licensing Requirements for Network Object NATThe following table shows the licensing requirements for this feature:ModelLicense RequirementASAvStandard or Premium License.All other modelsBase License.Prerequisites for Network Object NATDepending on the configuration, you can configure the mapped address inline if desired or you can create a separate network object or network object group for the mapped address. Network object groups are particularly useful for creating a mapped address pool with discontinous IP address ranges or multiple hosts or subnets. To create a network object or group, see the general operations configuration guide.For specific guidelines for objects and groups, see the configuration section for the NAT type you want to configure. See also the section.

Guidelines and LimitationsContext Mode GuidelinesSupported in single and multiple context mode.Firewall Mode Guidelines. Supported in routed and transparent firewall mode. In transparent mode, you must specify the real and mapped interfaces; you cannot use -Any-. In transparent mode, you cannot configure interface PAT, because the transparent mode interfaces do not have IP addresses.
You also cannot use the management IP address as a mapped address. In transparent mode, translating between IPv4 and IPv6 networks is not supported. Translating between two IPv6 networks, or between two IPv4 networks is supported.IPv6 Guidelines. Supports IPv6. See also the.
For routed mode, you can also translate between IPv4 and IPv6. For transparent mode, translating between IPv4 and IPv6 networks is not supported. Translating between two IPv6 networks, or between two IPv4 networks is supported. For transparent mode, a PAT pool is not supported for IPv6.
For static NAT, you can specify an IPv6 subnet up to /64.
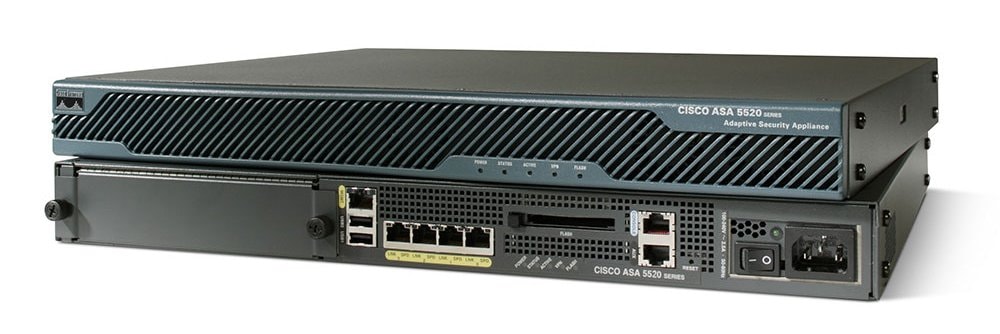
Contents.Reception and criticism Cisco ASA has become one of the most widely used firewall/VPN solutions for small to medium businesses. Early reviews indicated the Cisco GUI tools for managing the device were lacking, but that the device was otherwise impressive.A security flaw in Clientless Secure Sockets Layer Virtual Private Networking was rectified in 2015.A security flaw in a WebVPN feature was fixed in 2018.In 2017 revealed the existence of two privilege escalation exploits against the ASA called EPICBANANA and EXTRABACON, and a code insertion implant called BANANAGLEE, that is made persistent by JETPLOW. Features The 5506W-X has a WiFi point included.Architecture The ASA software is based on Linux. It runs a single Executable and Linkable Format program called lina. This schedules processes internally rather than using the Linux facilities. In the boot sequence a boot loader called ROMMON (ROM monitor) starts, loads a Linux kernel, which then loads the linamonitor, which then loads lina. The ROMMON also has a command line that can be used to load or select other software images and configurations.
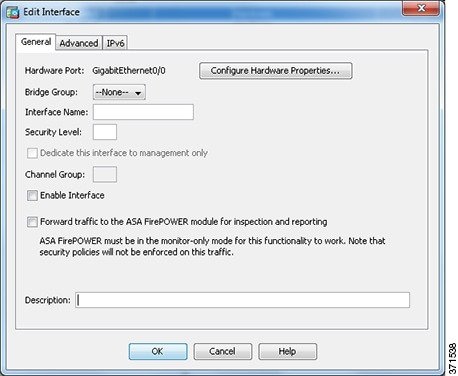
Cisco Asdm 7.2(1)
The names of firmware files includes a version indicator, -smp means it is for a symmetrical multiprocessor (and 64 bit architecture), and different parts also indicate if or is supported or not.The ASA software has a similar interface to the software on routers. There is a command line interface (CLI) that can be used to query operate or configure the device. In config mode the configuration statements are entered. 2012-12-04 at the quote: 'Las Vegas (Interop) May 3, 2005 – Cisco Systems, Inc., today announced the availability of the Cisco ASA 5500 Series Adaptive Security Appliance s'. Davis, David (19 February 2008).
TechRepublic. Davis, David (30 June 2005). Retrieved 21 March 2018. Retrieved 28 December 2012. Retrieved 28 December 2012. Saarinen, Juha (February 20, 2015).
Retrieved March 20, 2018. Saarinen, Juha (30 January 2018). Musalbas.com. ^. 9 February 2018. Retrieved 20 March 2018.
Moraes, Alexandre M. Cisco Press.
7 June 2017. Carroll, Brandon (January 5, 2011). Network Computing. 9 July 2006. Network Computing. 5 October 2010.
^. Retrieved 2008-05-15.External links.